A website get hacked via three end as follows :
- End User / Client End get hacked.
- Website Attacks and Hackers.
- Server Attacks and Hacked.
End User / Client End get hacked:
A client or user system get hacked that have website credential or website control credential. In that case there is not having any technology to prevent to use right credential for the website. How do server or website detects that credential enter by right Client or User or anthor unauthentic User. That kind stealth of credential by any user that around right user.
Website Attacks and Hackers:
The majority of websites are getting hacked because of either a poorly coded / insecure application or an outdated apps/script. The hackers / attackers are always learning new techniques and finding ways to exploit weaknesses in applications and websites. A protection layer to prevent vulnerabilities being exploited, making almost impossible to take advantage of loophole in website code as follows:
- XSS, CSRF/XSRF, SQL Injection Attacks.
- Cookie/Session Hijacking.
- Web Intrusion Prevention.
- Java script/iframe inserts/hacks.
- Brute Force Admin Login Attack Protection.
- Prevents Malwares, Trojan's & Badwares
- Getting infected by utilizing pattern recognition as well as signature definitions.
- Prevents listing in Google and Other blacklists.
- Trojan/ Malware Infection Prevention.
- Realtime Virus and Malware Protection.
- Protection from Spam Bots (Comment Spam).
 Server Attacks and Hacked:
Server Attacks and Hacked:
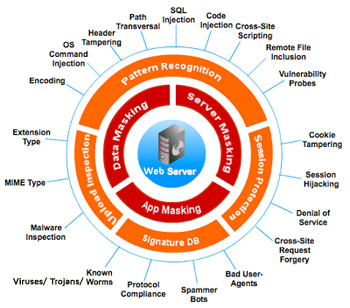
In picture, you can see layers of attacks on server, to get enter in server. Server attacks can be possible by any one above attacks or networks attacks. If a website get hacked that also give credential or control of server to attackers. So, that we need multiple security and prevention scheme to protect server as well as protect application Data. This security scheme can be define as as follows:
- First of all secure application code, that is strongly recommended. If code has security loophole, then attackers can get enter in server and can crashed whole server. This can be possible through virtualization of application root folder and application server.
- Second is Secure Data, that is also secondry recommended. If application get hacked, attackers can not misuse the data. This can be possible through encryption of codding as well as encryption of data.
- Third is network security. If network is not secure then hackers can apply many techniques to crack server credential or server security. In that case we should required to protect network through using network security techniques and equipments like Firewall, Network Antivirus, Router Security, Path security, Port Security etc.
- Last but not least is users or clients must be secure that have server credential or server access. Hackers can get access of server through get control of users or clients personal system.
We have lots of techinques to protect server form attackers and hackers as follows:
- Server Masking.
- Database and Files Masking.
- Application Masking.
- Upload Inspection.
- Pattern Recognition.
- Session Recognition.
- Signature Database.
- SQL Injection.
- Code Injection.
- Cross-site Scripting.
- Remote file Inclusion.
- Vulnerability Probes.
- Path Transversal.
- Header Tempering.
- OS Command Injection.
- Encoding.
- Extension Type.
- MIME Type.
- Malware Inspection.
- Known Virus / Trojans / Worms.
- Protocol Compliance.
- Spammer Bots.
- Bad User Agents.
- Cross Site Request Forgery.
- Denial of Service.
- Session Hijacking.
- Cookie Tempering.
Created: 05-May-2024 09:09 PM
Last Update: 2024-05-05 09:09 PM